PNPT Experience
Introduction
This blog post was written to help provide information and express my feelings about studying for and taking the Practical Network Penetration Tester (PNPT) exam by TCM Security.
The reason I decided to take this exam was because I felt that I struggled with Active Directory Pentesting and this exam offered a means for me to improve in that area and help me to level up as a pentester. I currently work on external pentests, web application pentest, and external red team pentest. However, I also wanted to acquire the skills needed to work on internal pentesting.
I bought the exam and training material for $400. One major plus for the PNPT is that it felt like the first exam I have taken that I would be confident in saying that the course material is all you really need in order to pass the exam. The study material points to other references for reading or practicing your skills, so I did not feel the need to buy anything else to study.
One more thing I would like to highlight before I get into the study material is the material and exam take a real world approach. The biggest hurdle some might have to overcome is to not treat this like a CTF and to instead treat it like a real engagement. As someone that does penetration testing for a living, this exam and study material hit the mark.
Study Material
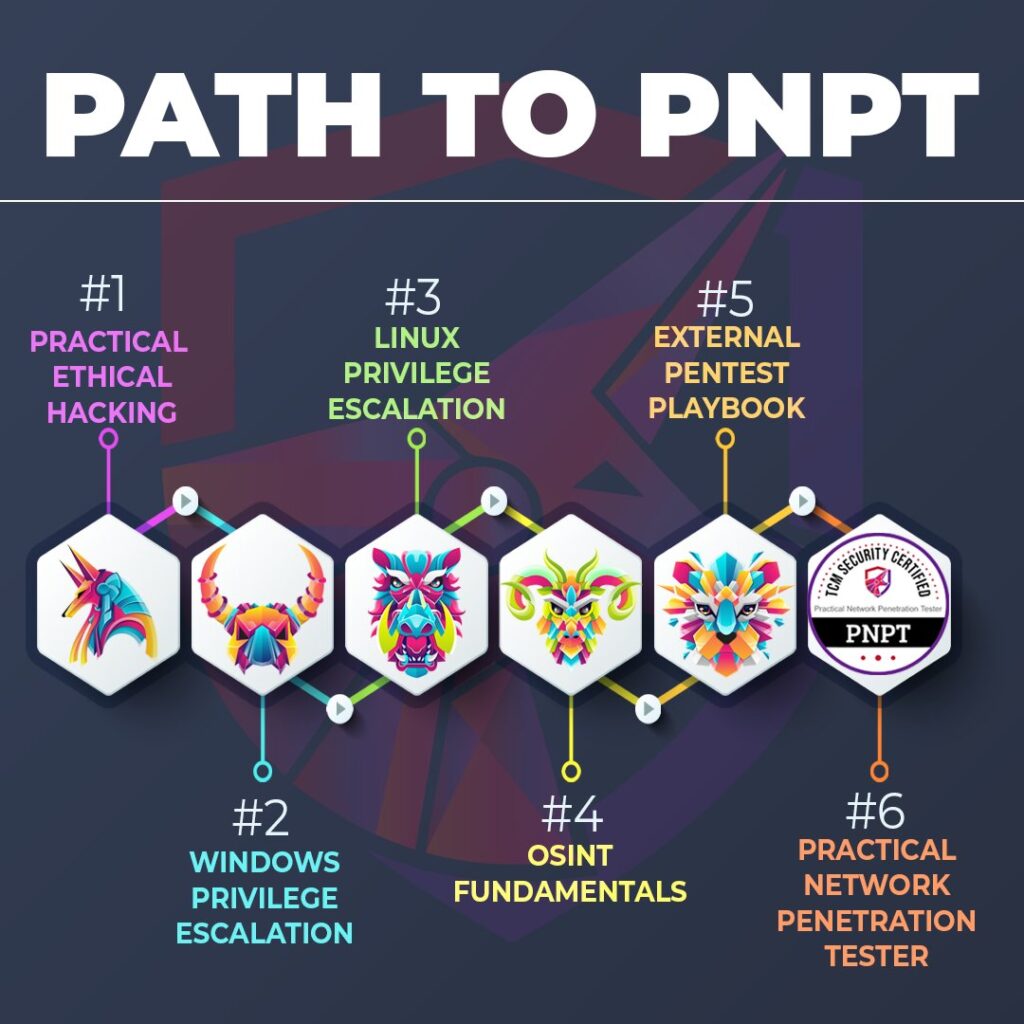
The Practical Ethical Hacking course is a great resource packed with essentials information. The material includes:
- Basic Networking
- Introduction to Linux
- Introduction to Python
- Information Gathering
- Vulnerability Scanning
- Buffer Overflows
- Active Directory
- OWASP Top 10
- Wireless Penetration Testing
- Report Writing
My attention was purely on the Active Directory portion of the material and what I spent the majority of my time on. However, I want to stress that I used the Buffer Overflow material here to ready myself for the eCPPT and for the eventual OSCP. TCM Security offers courses I would argue could replace other vendors’ study materials.
Going through this should help give someone the basic knowledge of penetration testing.
The Windows Privilege Escalation course is packed with excellent material and might have been my favorite course to go through. The course will cover:
- Kernel Exploits
- Stored Passwords
- Potato Attacks
- Registry
- DLL Hijacking
- Service Permissions
- Capstone Challenges to test knowledge of Windows Priv Esc. via Hack the Box and TryHackMe.
The Linux Privilege Escalation course will help provide material on how to escalate privileges on a linux host. I want to say that I truly appreciate the inclusion of capabilities and Docker. The course includes:
- Kernal Exploits
- Enumeration
- File Permissions
- Sudo
- SUID
- Capabilities
- Scheduled Task
- Root Squashing
- Docker
- Similar to Windows, you will get Capstone Challenges via Hack the Box and TryHackMe.
The OSINT Fundamentals course provides material on how to gather information about a target. This provides a real world engagement feel on encountering a target and gathering all the information information about that target. The course will teach you how to hunt down:
- Emails
- Passwords
- Usernames
- Social Media Accounts including
- LinkedIn
Instagram
- Website OSINT
- Using tools to gather information
- Report Writing
The final course is the External Pentesting Playbook. This material is designed to help show what pentesters do when attacking an external network. It goes against the CTF style of just checking exploits at a machine and seeing what sticks. It has a focus on:
- Attacking Login Portals
- Office 365
- OWA
- Standard Login Portals
- Insufficient Encryption
- Username Enumeration
- IKE Aggressive Mode
- Insufficient Traffic Blocking
- Open Mail Relays
- Client Debriefs
The Exam
The exam’s structure gives you five days with the exam lab and then two days to write a professional report. After writing the report you will submit it for review and if you meet the objectives you will get an email to schedule a time to do a fifteen minute debrief over the report. Again capturing that real world feel of talking to a client and going over the report and findings. You can use whatever tools you want for the exam.
When the exam started I was given all of the information needed to complete the exam including what objectives need to be met and a sample report to help show how the final report should be structured.
TCM Security provided a stable and solid network to attack. This was a breath of fresh air after working on the eCPPT and eWPT this year, with their unstable exam environments that were unusable for hours.
As I moved through the exam environment I took breaks, ate meals, spent time with my family, and rested my mind when I needed to. I would get stuck a few times, but I felt the exam did a good job of rewarding for enumerating, taking good notes on the findings, and using that information in the exam. I never felt frustrated, which is a great feeling taking a major exam.
The best advice I can give is:
- Know and understand the study material and do the labs provided by TCM Academy.
- Feel confidant in Active Directory Attacks.
- Know how to write a good and professional report.
- Understand the exploits and how to remediate them.
- Read through the provided information from TCM Security thoroughly and understand what you can and cannot do.
Final Thoughts
I really enjoyed this exam and the content provided by TCM Security through TCM Academy. I learned a lot going through it and had a lot of fun doing the exam. It’s one of the exams I would do over again just because I felt it was a lot of fun. The report writing is always the boring part, but the exam was great. I truly enjoyed this experience and the fact that it captures the feel of a real life pentesting engagement.
I hope more pentesters and aspiring pentesters look into TCM Security as a budget friendly and quality training material and wish you luck on the exam if you choose to take it!
If you found this helpful, please send me a tweet and tell me what you thought! Feedback is always appreciated!
Good luck!